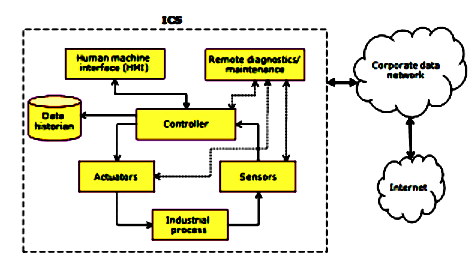
Industrial Control System (ICS) is a general term used to describe the integration of hardware and software with network connectivity in order to support critical infrastructure.
ICS technologies include, but are not limited to, supervisory control and data acquisition (SCADA) and distributed control systems (DCS), industrial automation and control systems (IACS), programmable logic controllers (PLCs), programmable automation controllers (PACs), remote terminal units (RTUs), control servers, intelligent electronic devices (IEDs) and sensors.
Historically, most machinery and engineering components used in manufacturing and the operation of power plants, water and wastewater plants, transport industries and other critical infrastructures were dumb, and those that were computerized typically used proprietary protocols.
The networks they belonged to were air-gapped and protected from the outside world. This has changed over the years and components of today’s ICSs are often connected directly or indirectly to the internet.
Advances in smart sensor technology and wireless networking have made the blending of operational technology (OT) with information technology (IT) desirable and cost-effective.
Despite the benefits of increased speed, better responsiveness to conditions and improved reliability that IT/OT convergence had brought, however, there are drawbacks in terms of security.
Targeted attacks against ICSs by terrorists pose a threat to most nations around the world. As remote telemetry units used to input change become more capable of local control and as the Internet of Things (IoT) and Industrial IoT continue to grow, it becomes increasingly important for strategies to protect ICSs from security threats be top of mind.
In the United States, the Department of Homeland Security (DHS) has offered these recommends for protecting industrial control systems:
- Use application whitelisting to protect infrastructure from potentially harmful programming.
- Implement configuration management and patch management controls to keep control systems secure.
- Reduce attack surface areas by segmenting networks into logical parts and restricting host-to-host communications paths.
- Require multi-factor authentication and enforce the principle of least privilege (POLP).
- Require remote access to be operator controlled and time limited.
- Monitor traffic within the control network and on ICS perimeters.
- Analyze access logs and verify all anomalies.
- Ensure the restore includes golden records so systems can be rolled back to last known good state.
DHS said Russian hackers first targeted key industrial control vendors in order to steal credentials and access air-gaped and isolated utility networks.